Public safety is of concern for all countries, with teams spending hours working tirelessly to ensure that citizens are protected. Such incidents include natural disasters, crime spikes, or any unrest that may occur. In 2017, several African countries were hit by unforeseen disasters. These included floods in Nigeria and Niger, the Sierra Leonne mudslides and devastating fires in both Kenya and South Africa. In these times of crisis, technology has a crucial role to play in ensuring that public safety teams can effectively communicate in real time to mitigate the impact of disasters and reach the concerned sites on time.
According to Jan Liebenberg, Head of Market and Business Development for Nokia Southern Africa, 3GPP mobile technology will become an even more critical component, not only in connecting a specific public safety team but also ensuring interconnectivity between different teams to improve situational awareness.
“Typically, today, the police, fire brigade and ambulance services don’t have connectivity between each other,” he said.
“Each emergency service has their own network or their own voice communications system and might not share a command and control centre.
“With the adoption of mobile broadband technology, public safety networks can benefit from the advantages of interconnectivity, fast and reliable broadband data and real-time video services, opening new communications possibilities for rescue missions and disaster recovery situations.
“This will enable them to call, listen or share information with each other to get a better grasp of their operational environment, improve real-time collaboration and co-ordination when the situation requires urgent attention.”
In an ideal world the different public safety teams would be able to communicate across a single, secure network, but, this is not always the case, particularly when legacy networks are involved.
“We can maintain the old networks and start to enhance those networks by adding newer technology with updated functionalities and then gradually phase out the older networks,” added Liebenberg.
“So, from a total cost of ownership perspective, the old assets that have already been invested in are maintained, while new capabilities are added gradually.
“In this way we don’t have to replace the complete public safety network environment in one big step.
“In parallel to the voice services, that the current public safety networks offer, we also offer high-quality real-time video feed services. This real-time video feed of situations can be viewed by the control centre or teams travelling to a scene, helping them prepare for arrival or to offer better support.
“We can also overlay additional data services such as rapid database access, location-based services or bio vital monitoring to remotely activate a responder’s cameras and monitor their vital signs to check their safety. Text communication and push-to-video (PTV) capabilities are also supported, allowing for a broadcast text/video communication to all public safety teams to ensure that everyone is informed of developments in real time.”
Certain natural disasters could cause network outages, but there are solutions for those.
“In areas where the existing network is not available, for example, if there has been an earthquake, we have the capability to establish a portable public safety network for the first responders,” explained Liebenberg.
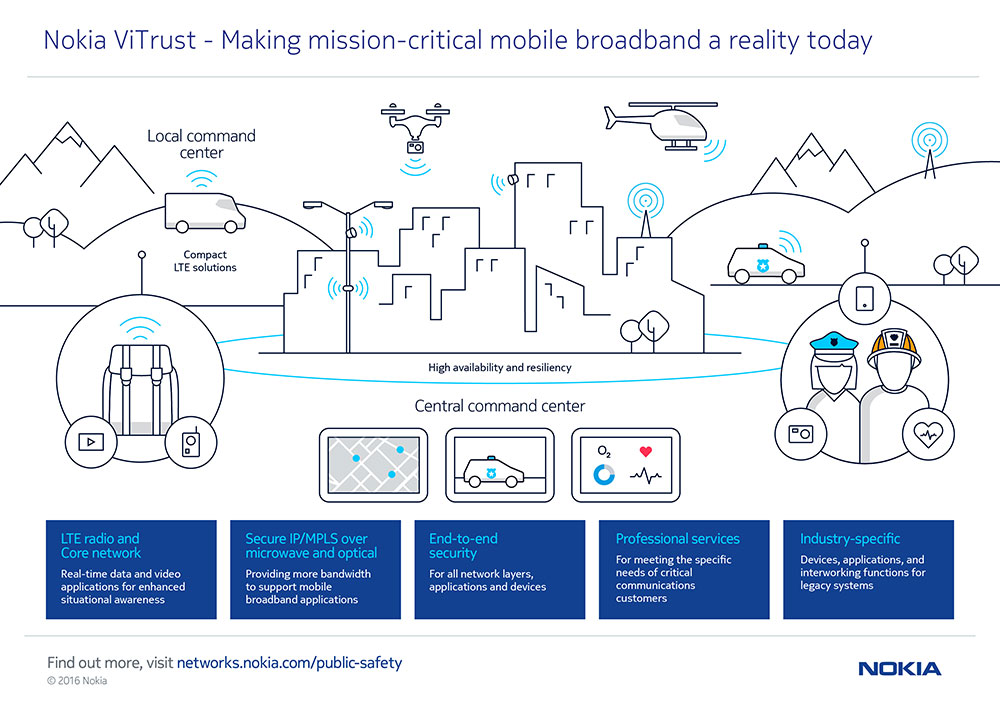
“Ultra-Compact Network is the smallest unit and can be carried in a backpack or transported in a regular-sized vehicle such as a police car. It comprises radio, core and applications such as Group Communications, including push-to-talk and push-to-video capabilities and can integrate other high-bandwidth mission-critical services such as video analytics and geo-location.
“This enables the first responders to set up their own secure broadband communication network instantly, allowing them to communicate with each other, ensuring nowhere is too remote for them to protect the public and save lives. Additionally, new technologies, such as drones, can be used as part of the public safety network. These drones can be used to assist in identifying hotspots or searching for missing persons.
“When more accurate information is available to the public safety workers, they are able to respond and distribute crucial information faster. This is particularly important when missing people are involved. Information can be provided in a faster, more dynamic way, enabling them to deliver better results and a better service to citizens.”
Analytics is another way to improve the network to deliver intelligence, without requiring human intervention.
“By using analytics, specific areas can be monitored, alerts issued and teams dispatched when needed,” said Liebenberg.
“For example, if there is flooding and the water rises to a specific level, analytics overlaid on standard CCTV cameras can analyse the changing environment, raise the necessary warnings and dispatch the required teams. Crime hotspots can also be monitored in a similar way, when for example abnormal crowd movement is detected, the required teams could be automatically dispatched. This could completely revolutionise public safety on the continent.”
With an enhanced public safety network, a consolidated database containing big data can be created. Data in the database will for example include information on: incidents, resolutions, environmental sensors, weather patterns, video feeds, etc. Analytics can also be applied on the big data in the database to determine for example crime patterns and hotspots, traffic flow patterns or air quality information, thus allowing statistical information to be available and preventative measures to be applied if required.
Cyber-attacks are a growing threat to all types of mission critical networks, including those used by all emergency services. In most African countries, governments are starting to realise the importance of security and discussion around Cyber Security policies are in the works. In South Africa, the government is in the process of establishing a Cybercrimes and Cybersecurity Bill.
Liebenberg says that today’s networks have evolved and that security is at the core of the network. “Public safety networks are often private networks, which means they are only accessible by the public safety workers via their special devices, SIM cards, and authentication mechanisms,” he said.
“That is the first layer of security. Secondly, the security solutions that we deploy on these networks monitor unauthorised connectivity. If a public safety worker loses their device, those devices are typically blocked from the network to restrict any unauthorised user access. The devices are also secured with passwords or lock codes, so a lot of security mechanisms are deployed, and, on the backend, our security solutions monitor and track all the devices.
“All the information that is distributed to the public safety workers needs to be accurate, so it’s important to make sure the network is as secure as possible. Different levels of access and authorisation is created in the network and this is all planned upfront as part of the public safety network design phase.
“So, there is a lot of security architecture features that are included, such as security automation that encompasses business processes, incident response plan, regulations and policies, end-to-end security that encompasses the operation of the network and its processes, security analytics to correlate security-related information from across the network, devices and applications to spot suspicious anomalies and provide insight into threats and multi-layer encryption to protect network traffic. Such a multi-layered and active security approach provides the right balance of costs with the in-depth protection needed to defend against today’s security threats.”
Nokia’s end-to-end approach brings simplicity to public safety network deployment and provides a solid foundation for developing mission-critical communications. The introduction of 3GPP mobile technologies for mission-critical mobile broadband requires careful preparation to ensure a smooth transition and includes evaluation of current and future applications, finding the right deployment model and identifying assets and gaps.
Click below to share this article